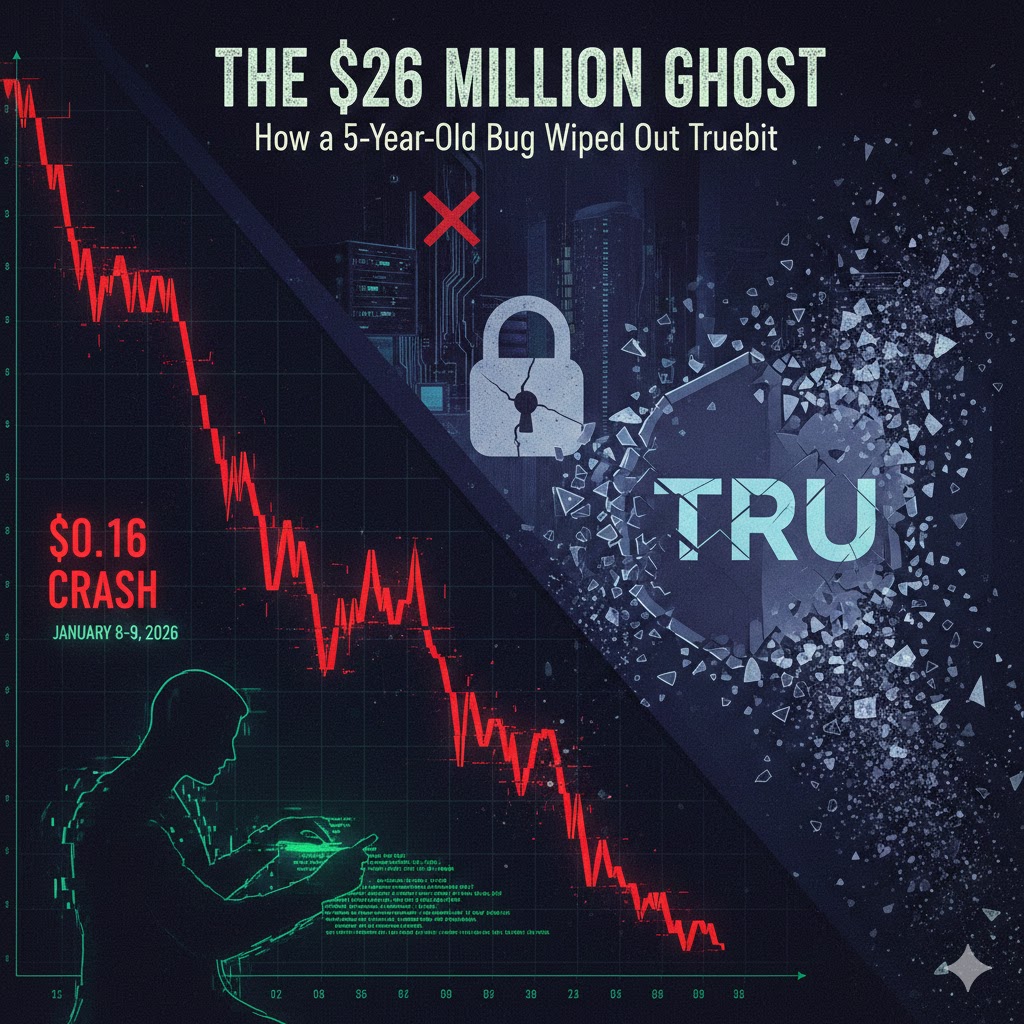
On January 8–9, 2026, the Truebit protocol, a long-standing Ethereum-based verification and computation project, suffered a devastating security exploit. The attack resulted in the theft of over 8,535 ETH (approximately $26.6 million) and caused the protocol’s native token, TRU, to plummet more than 99.9% in value.
The incident serves as a stark warning about the risks associated with “legacy” smart contracts that remain active years after their initial deployment.
🛡️ The Anatomy of the Exploit
The breach targeted a specific, five-year-old smart contract that had remained operational since the project’s early days. Unlike many modern DeFi protocols that utilize open-source code for public auditing, this particular contract was closed-source, which may have helped the vulnerability remain hidden for years.
The Vulnerability: Arithmetic Logic Flaw
According to security researchers at Beosin and PeckShield, the attacker exploited an arithmetic logic error (likely related to integer truncation) within a specific minting function.
-
Discounted Minting: The flaw allowed the attacker to call a purchase function with a negligible amount of ETH (a near-zero
msg.value) while still receiving a massive amount of TRU tokens. -
The Drainage Loop: Once the attacker possessed millions of “free” TRU tokens, they utilized the protocol’s burn function. This function was designed to let users sell tokens back to the protocol in exchange for ETH from its reserves.
-
Liquidity Extraction: By repeatedly minting tokens for nothing and burning them for ETH, the attacker effectively drained the protocol’s treasury. Reports indicate the process was repeated several times, with the ETH amount increasing in each iteration until the reserves were empty.
📉 Market Impact: The Death of TRU
The financial fallout was immediate and catastrophic for TRU holders.
-
Price Collapse: Before the hack, TRU was trading at approximately $0.16. Within hours of the exploit, the price collapsed to $0.00000000072, essentially wiping out the token’s market capitalization.
-
Liquidity Crisis: As the attacker “sold” their minted tokens into the protocol, the ETH liquidity backing the TRU token vanished. This left legitimate investors unable to exit their positions, as there was no longer any value remaining in the bonding curve.
⚖️ The Official Response
Truebit acknowledged the incident via social media, stating they were “aware of a security incident involving one or more malicious actors.”
-
Investigation: The team has confirmed they are coordinating with blockchain security firms and law enforcement to track the stolen funds.
-
Fund Tracking: On-chain data shows the stolen 8,535 ETH was moved to several high-risk wallets. Interestingly, security analysts noted that one of the attacker’s addresses was linked to a previous exploit of the Sparkle Protocol just weeks prior.
-
User Warning: Truebit has advised all users to cease interaction with the affected legacy contracts immediately while the investigation continues.
💡 Lessons for the DeFi Space
The Truebit exploit highlights a growing trend in 2025 and early 2026: Legacy Contract Targeting. As security standards for new contracts improve, malicious actors are increasingly scanning the blockchain for “forgotten” code—contracts deployed years ago that lack modern security features like emergency pauses, SafeMath libraries, or updated Solidity compiler versions.
Key Takeaway: For developers, this event underscores the necessity of “decommissioning” or upgrading old contracts. For investors, it is a reminder that even “battle-tested” protocols can have hidden vulnerabilities in their oldest layers.